Sql Server Can Windows Nt Service Impersonate Sql Server Login Updated FREE
Sql Server Can Windows Nt Service Impersonate Sql Server Login
By: | Updated: 2017-10-12 | Comments (8) | Related: More than > SQL Server on Linux
Problem
You want to use Linux for some of your SQL Server instances, simply you are worried virtually the administrative overhead related to using SQL Server authentication on those new Linux servers. In this tip I volition explain how to use Windows Authentication for your SQL Server instances running on Linux.
Solution
One of the responsibilities for a Database Administrator (DBA) is to ensure the security of our databases. It is pointless to comply with the To the lowest degree Privilege Principle (https://world wide web.us-cert.gov/bsi/articles/knowledge/principles/least-privilege) if y'all take your password written on a Postal service It at your monitor or below your keyboard. Nosotros all know that our capability to call back passwords is limited; nowadays people have lots of passwords to recollect like e-mail, ATM code, social networks, etc. just to mention a few.
If you ever had a chance to piece of work at a visitor with more than threescore servers it will exist impossible to recollect each server password for the sa user business relationship, especially if we must comply with a password policy regarding complexity and expiration.
Fortunately we can utilize Windows Authentication on our servers and just remember our Windows login business relationship password to administer all the servers in our infrastructure; fifty-fifty the Linux database servers.
Using Active Directory Authentication with SQL Server on Linux
In order to use Active Directory Hallmark for an SQL Server running on Linux we must configure the Linux server network and join it to our domain controller realm. Since most of us as SQL Server administrators are new to Linux I am explaining the very basics.
Checking Network Interface and Host Name
This is the very first step. We must make sure that our Linux server is on the same network of the Domain Controller and the server can resolve the Domain Controller name. So we must check the network interface, the domain controller and our server�s host name. If yous are very new on Linux, y'all should know that on Linux all configurations are kept in text files. To modify the network configuration of our Linux server we must edit the file /etc/network/interfaces as root.
nano /etc/network/interfaces
On the following image you can get an idea of what yous will run across. Observe that I marked with different colors the loopback device configuration and the Ethernet configuration, which is the one we have to alter.
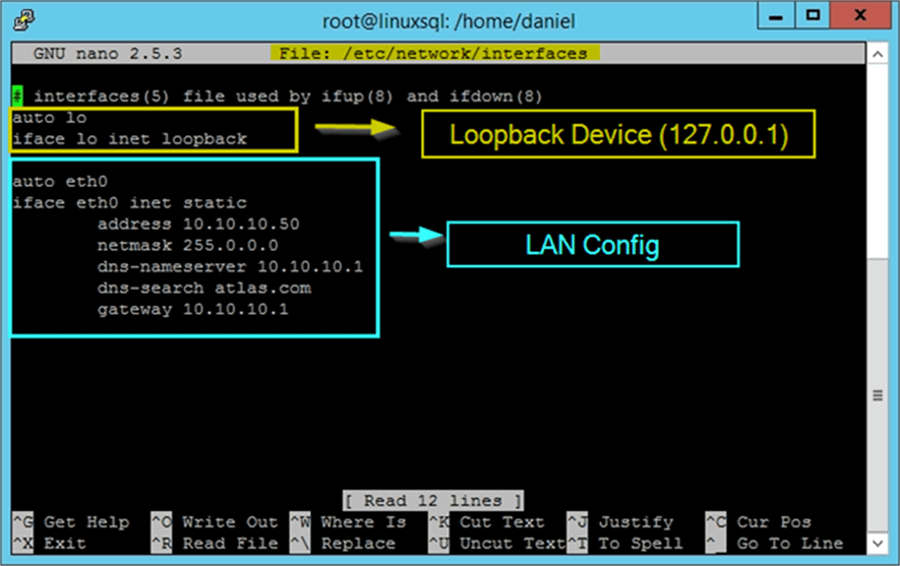
The outset line of the LAN Configuration is to instruct the operating system to bring the eth0 interface upwardly at kick fourth dimension. On the next lines we must enter the parameters for the network adapter configuration. In my case I am non using a DHCP server, so I have set the interface as static. Otherwise my eth0 interface will exist every bit it follows:
auth eth0 iface eth0 inet dhcp dns-nameserver ten.10.10.1 dns-search atlas.com
After modifying that file you should restart the network interface to see the changes.
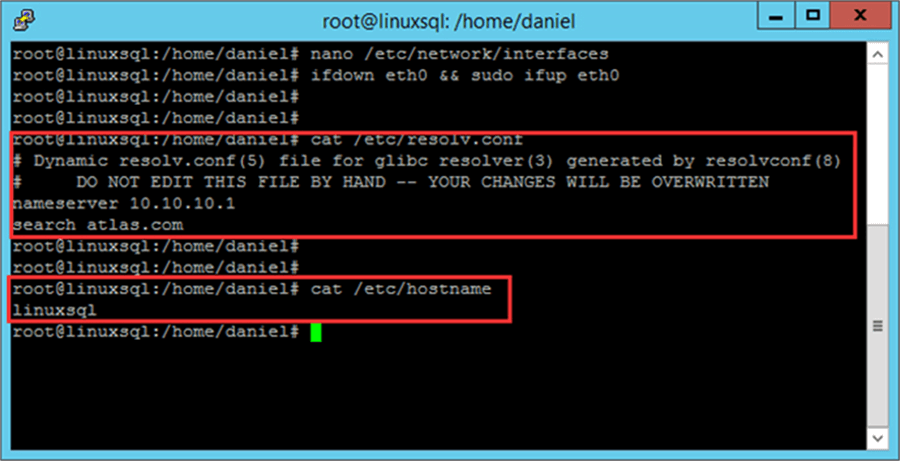
ifdown eth0 && sudo ifup eth0
Now check that you are using the right DNS server. This file should not be edited past manus
If you need to modify your Linux server proper name yous accept to edit the file /etc/hostname and restart the figurer.
Installing Required Packages and Joining to Agile Directory
There are a few packages needed to bring together a Linux Server to Active Directory. In order to install them we utilise apt-get control as follows.
apt-become install realmd krb5-user software-properties-common python-software-backdrop packagekit sssd-advertising samba-mutual-bin samba-libs sssd-tools krb5-user adcli
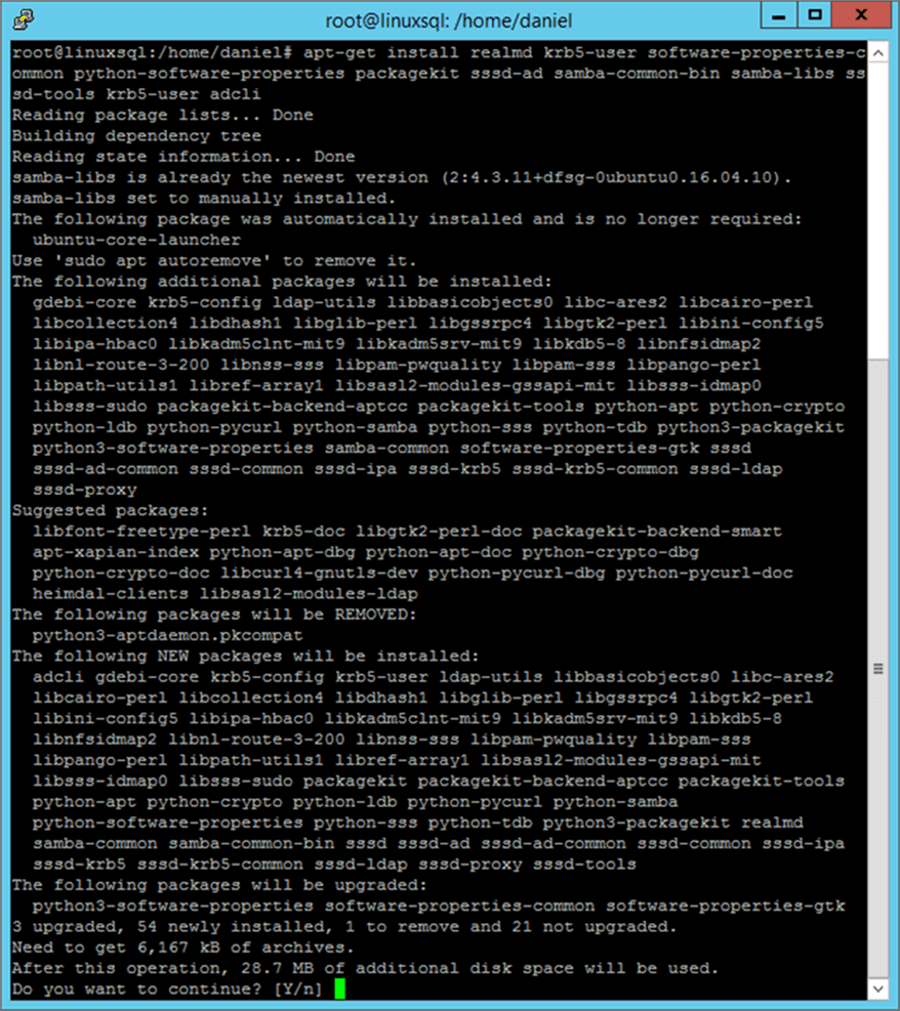
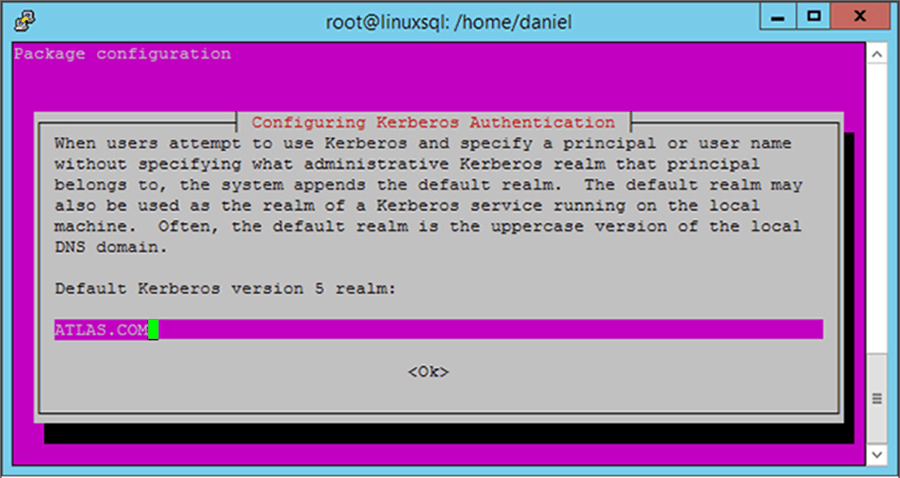
Afterwards yous confirm the installation of these packages you lot will exist asked to prepare your Default Kerberos version five realm. You must enter your domain controller in uppercase.
Although it is not strictly required, it is a good practice to install and configure the NTP (Network Time Protocol) service to get the server�s time synchronized with the domain controller. To install this service we use our parcel director.
And so edit the /etc/ntp.conf file and comment out the preset timeservers and add your Domain Controller.
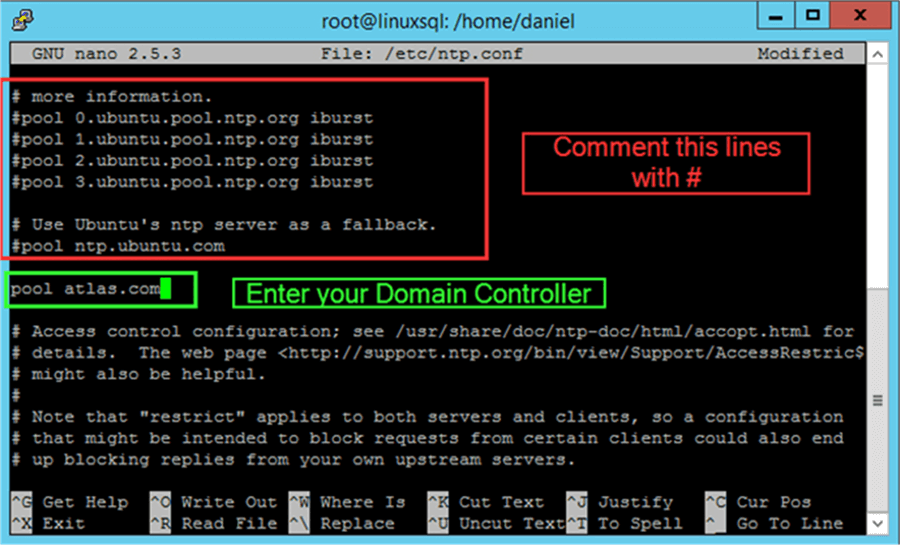
Finally we must restart the ntp service.
Configuring realmd
Nosotros must create a file named /etc/realmd.conf. This file will agree the configurations that will let our Linux server to properly annals into our Domain Controller. To create this file I am using the nano editor as shown before.
When the editor opens paste the following configuration, but alter the values equally needed, particularly the domain proper name.
[users] default-dwelling = /dwelling house/%D/%U default-shell = /bin/bash [active-directory] default-client = sssd os-proper name = Ubuntu Linux os-version = xvi.04 [service] automatic-install = no [atlas.com] fully-qualified-names = no automatic-id-mapping = yes user-main = aye manage-system = no
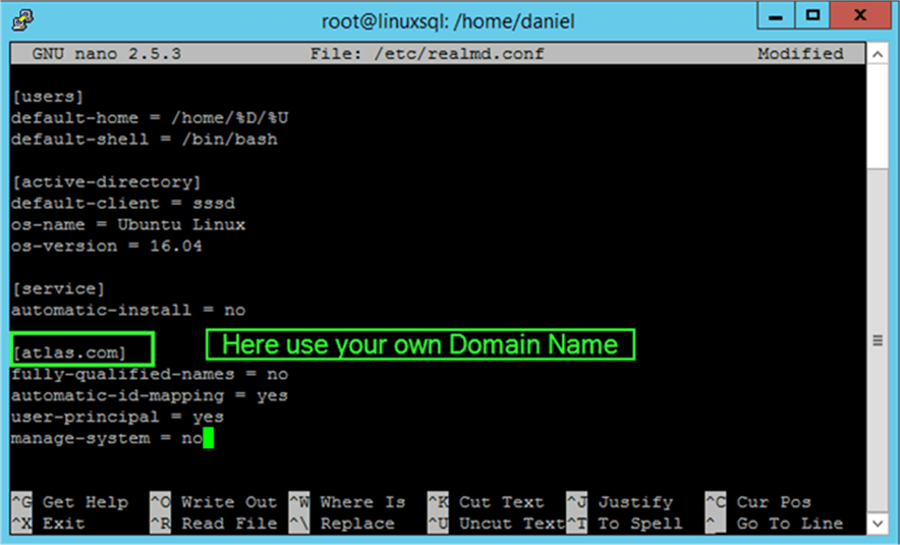
After saving the file we must restart the realmd service.
Joining the Linux Server to Active Directory
Now finally we are gear up to join our Linux server into Active Directory. To do and so we have to use the realm control:
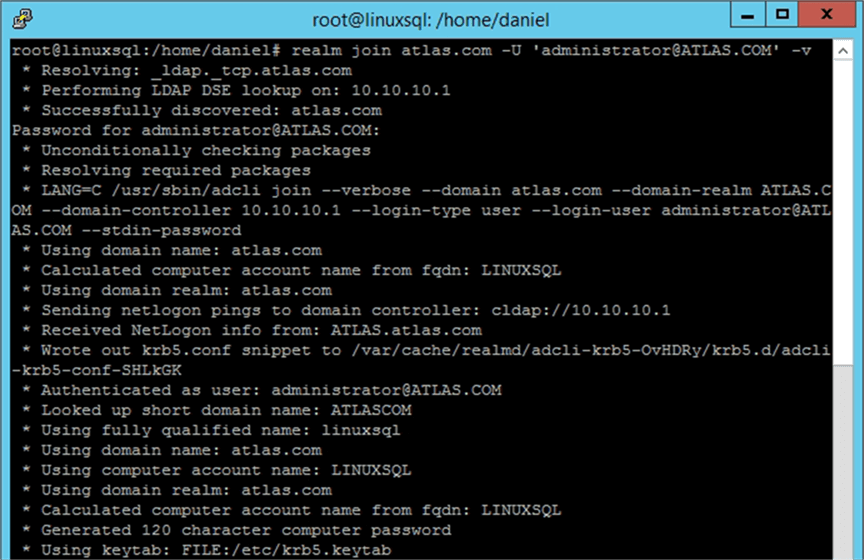
realm join [your_domain.com] -U '[user_with_rights_to_add_computer_to_domain@YOUR_DOMAIN.COM]' -v
On the previous command, I enclosed with brackets the parameter�s values you lot need to change according to your environs. Notice the fact that I used capitalized letters for the domain, this is required. In my example the previous command is as follows:
realm bring together atlas.com -U 'ambassador@ATLAS.COM' -v
You will be asked for the password of the domain account used to join the server into Agile Directory. In my example information technology is the password for the administrator@ATLAS.COM account.
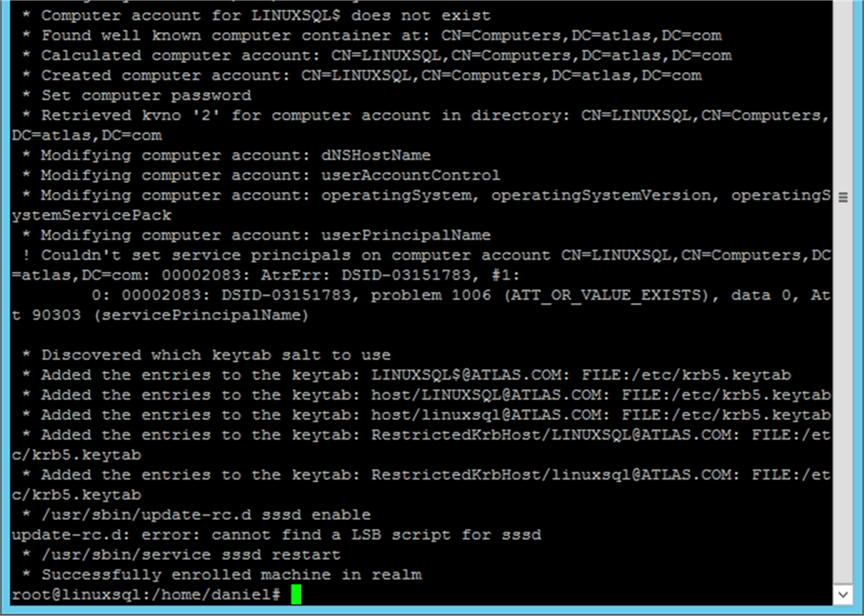
The post-obit images shows screen capture of what yous may look to see.
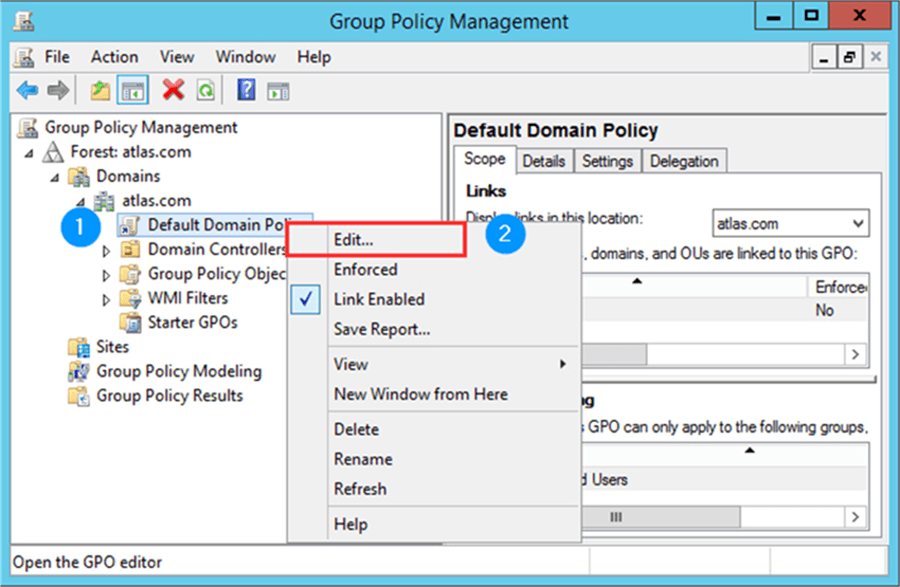
Creating a SQL Server Service Account
We need to create an Active Directory account for our SQL Server service. Merely to remind y'all, using an business relationship with domain admin rights is a very bad practise. Remember that the account must have the �Logon as a Service� permission enabled. In order to grant this permission to an account you should open the Group Policy Management console and select to edit the default domain policy as shown on the following image.
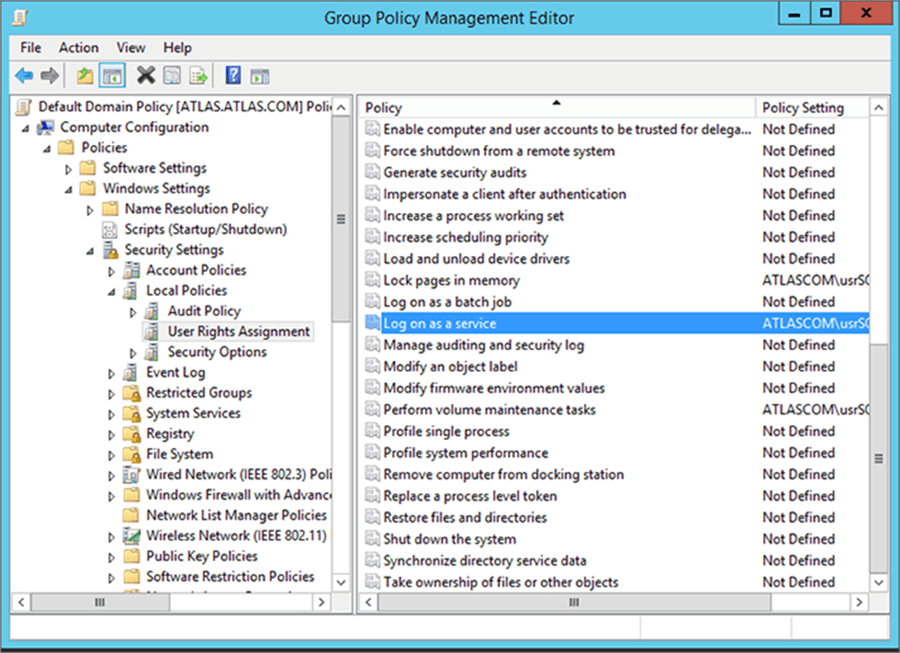
When the GPO Editor opens, in the console tree follow this path: Computer Configuration > Windows Settings > Security Settings > Local Policies > User Rights Assignment. And then in the right panel scan for the Logon equally a Service policy and add your service business relationship.
Creating the Service Master Name
Now nosotros must create the Service Principal Name (SPN) to associate our SQL Server instance with the service logon business relationship. In Windows this is washed automatically, but in Linux we have to exercise this past hand. If you want more information most SPN�s yous can take a look at the following MSDN page: https://msdn.microsoft.com/en-us/library/ms677949.aspx.
Service Principal Names take the post-obit syntax:
Service_Type_Identifier/Fully_Qualified_Domain_Name:Listening_Port
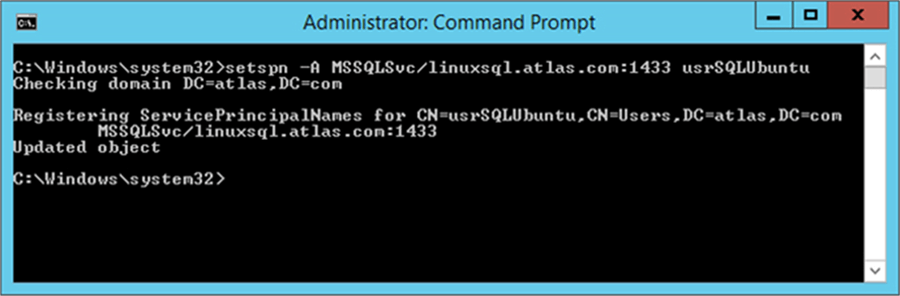
In social club to create the SPN we must use the setspn utility with the A switch (nosotros desire to add an SPN) on our Domain Controller. Too you can use any workstation who has this utility installed.
setspn -A MSSQLSvc/linuxsql.atlas.com:1433 usrSQLUbuntu
The image below is a screen capture of the previous control execution.
Creating the Keytab File for the SQL Server Service
A keytab file contains pairs of Kerberos principals and encrypted keys. Nosotros have to apply a keytab file to authenticate into Active Directory using Kerberos without entering a password. Something that is worth mentioning is that if you change the password you will need to recreate the keytab file again.
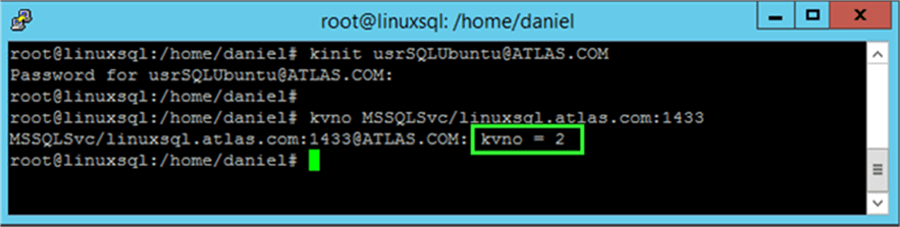
Our commencement step is to check and take note of the Key Version Number (kvno) for the Active Directory account we aim to use as the SQL Server service business relationship. To do so we must use the kinit tool get-go to obtain a Kerberos ticket for our service account. Of grade you lot will be prompted for the account�south password.
kinit usrSQLUbuntu@ATLAS.COM
Later entering the password and back into the prompt we are able to utilise the kvno tool passing our Service Main Proper noun as a parameter. Just in case, this is the same value we take registered on Windows.
kvno MSSQLSvc/linuxsql.atlas.com:1433
The post-obit is a screen capture of the previous command execution in my test environment. If everything is ok you should see something similar. Retrieve to keep annotation of the kvno, in my case information technology is 2.
Now with that done, we are fix to use the ktutil utility to create the keytab file.
This utility volition open a prompt displaying �ktutil:� in which nosotros have to enter the following commands. You lot will be prompted for the business relationship�s password.
addent -password -p MSSQLSvc/linuxsql.ATLAS.COM:1433@ATLAS.COM -thou ii -e aes256-cts-hmac-sha1-96 addent -countersign -p MSSQLSvc/linuxsql.ATLAS.COM:1433@ATLAS.COM -k 2 -e rc4-hmac write_kt /var/opt/mssql/secrets/mssql.keytab quit
Now I will proceed to explain what those commands hateful:
- Addent: Adds a principal to keylist using a key or a password. Every bit you tin can approximate, since we are using the �password switch, we are adding the principal with a countersign and you will be prompted for the master�south countersign. The �p, -k and �due east switches are used to specify the principal, the primal version number and the encryption type respectively. That being said, you lot may accept to modify the value subsequently the �k switch for the one you lot received with the kvno utility.
- Write_kt: Writes the electric current keylist into a Kerberos keytab file.
- Quit: Exits the ktutil utility.
Securing the Keytab File
Anyone who has access to the keytab file tin impersonate the service account, so information technology is a good practise to restrict the access to keytab file for the Linux account on which our service runs which by default is the mssql user.
chown mssql:mssql /var/opt/mssql/secrets/mssql.keytab chmod 400 /var/opt/mssql/secrets/mssql.keytab
With the chown command we are changing the buying of the keytab file to the mssql user which is in the group mssql.
The chmod 400 sets the keytab file permissions as read only for the possessor, which in this case is the mssql user. Needless is to say that no other user will be able to read this file other than mssql user or whatsoever other user with root rights.
Setting up Active Directory Authentication for SQL Server
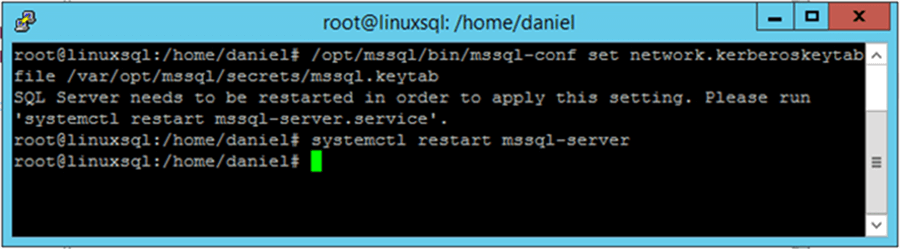
Finally nosotros must set our Linux SQL Server instance to utilise the previously created keytab file to authenticate into Active Directory. To do so, we utilise the mssql-conf utility equally follows.
/opt/mssql/bin/mssql-conf prepare network.kerberoskeytabfile /var/opt/mssql/secrets/mssql.keytab systemctl restart mssql-server
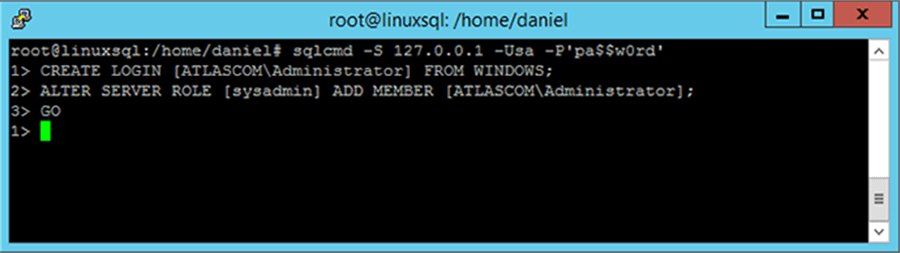
Assigning Permissions to an Agile Directory Business relationship
Now that we have our Linux SQL Server example joined into Agile Directory we have to connect to our instance and add together a domain account or group. I am doing so with the administrator account for simplicity, simply you shouldn�t use this account in production.
CREATE LOGIN [ATLASCOM\Administrator] FROM WINDOWS; ALTER SERVER Office [sysadmin] Add together MEMBER [ATLASCOM\Administrator]; Become
Side by side Steps
- If y'all don�t have SQL Server on Linux already installed check out the following tip that shows you how to install SQL Server on Ubuntu: Installing SQL Server vNext on Ubuntu.
- For more information about mssql-conf utility y'all tin can review this tip: Configure SQL Server on Linux.
- There are cases on Windows on which you also have to register the SPN by mitt. If that is your instance I suggest that you take a look at the post-obit two tips: Annals a SPN for SQL Server Hallmark with Kerberos and Get SQL Server SPN data for all servers using PowerShell.
- On the last screen capture I was using sqlcmd to connect to SQL Server. if you lot need to refresh concepts about sqlcmd you can take a expect at /sqlservertip/4923/introduction-to-sql-servers-sqlcmd-utility/.
Related Manufactures
Popular Articles
About the author
 Daniel Farina was built-in in Buenos Aires, Argentina. Self-educated, since childhood he showed a passion for learning.
Daniel Farina was built-in in Buenos Aires, Argentina. Self-educated, since childhood he showed a passion for learning.
View all my tips
Article Final Updated: 2017-10-12
Sql Server Can Windows Nt Service Impersonate Sql Server Login
DOWNLOAD HERE
Source: https://www.mssqltips.com/sqlservertip/5075/configure-sql-server-on-linux-to-use-windows-authentication/
Posted by: dunkinfousee1994.blogspot.com